As you might know, I love to combine several OpenSource tools to get things done. One thing I wanted to play for some weeks is Autotimeliner by Andrea Fortuna.This tool is made to extract events from an Memory Image to combine it into a timeline. If you have a timeline, what comes next? Of course, putting it into Timesketch. So let’s give it a try.
We start with a memory dump from a Stuxnet infection from https://github.com/ganboing/malwarecookbook. Download the four files, extract them and you are good to go.
Prerequisites
Volatility
Installation is pretty easy, install Volatility either via pre-compiled binary or install it manually, see the Volatility installation wiki for further information.
Test it running:
vol.py -vSleuthkit
To install sleuthkit run:
(You need that for mactime)
brew install sleuthkitor
sudo apt-get install sleuthkitInstallation Autotimeliner
Simply clone the GitHub repository:
git clone https://github.com/andreafortuna/autotimeliner.git
Run it
python autotimeline.py -f /Users/foobar/Downloads/stuxnet.vmem.zip/stuxnet.vmem -p WinXPSP2x86 -t 2009-10-20..2018-10-21That might take some time depending on your hardware.
Now you have an csv file around 5.6 MB.
_ _______ _ _ _
/\ | | |__ __(_) | (_)
/ \ _ _| |_ ___ | | _ _ __ ___ ___| |_ _ __ ___ _ __
/ /\ \| | | | __/ _ \| | | | '_ ` _ \ / _ \ | | '_ \ / _ \ '__|
/ ____ \ |_| | || (_) | | | | | | | | | __/ | | | | | __/ |
/_/ \_\__,_|\__\___/|_| |_|_| |_| |_|\___|_|_|_| |_|\___|_|
- Automagically extract forensic timeline from volatile memory dump -
Andrea Fortuna - andrea@andreafortuna.org - https://www.andreafortuna.org
*** Processing image /Users/foobar/Downloads/stuxnet.vmem.zip/stuxnet.vmem
-------
*** Using custom profile: WinXPSP2x86
*** Creating memory timeline......done!
*** Creating shellbags timeline......done!
*** Creating $MFT timeline......done!
*** Merging and filtering timelines......done!
Timeline saved in /Users/foobar/Downloads/stuxnet.vmem.zip/stuxnet.vmem-timeline.csvThe format used for the dates is not compatible with Timesketch:
more /Users/foobar/Downloads/stuxnet.vmem.zip/stuxnet.vmem-timeline.csv
Date,Size,Type,Mode,UID,GID,Meta,File Name
Tue Oct 20 2009 12:08:04,0,ma.b,---a-----------,0,0,84995,"[MFT STD_INFO] Python26\Lib\SITE-P~1\setuptools-0.6c11-py2.6.egg-info\TOP_LE~1.TXT (Offset: 0x8a28c00)"
Tue Oct 20 2009 12:08:04,0,ma.b,---a-----------,0,0,85000,"[MFT STD_INFO] Python26\Lib\SITE-P~1\SETUPT~1.EGG\DEPEND~1.TXT (Offset: 0x75e4000)"
Tue Oct 20 2009 12:08:06,0,m..b,---a-----------,0,0,84985,"[MFT STD_INFO] Python26\Scripts\EASY_I~1.PY (Offset: 0x91b9400)"
Tue Oct 20 2009 12:08:06,0,ma.b,---a-----------,0,0,84986,"[MFT STD_INFO] Python26\Scripts\EASY_I~1.MAN (Offset: 0x91b9800)"
Tue Oct 20 2009 12:08:06,0,ma.b,---a-----------,0,0,84987,"[MFT STD_INFO] Python26\Scripts\EASY_I~1.EXE (Offset: 0x91b9c00)"
Tue Oct 20 2009 12:08:06,0,ma.b,---a-----------,0,0,84988,"[MFT STD_INFO] Python26\Scripts\EASY_I~2.MAN (Offset: 0x1042f000)"
Tue Oct 20 2009 12:08:06,0,m..b,---a-----------,0,0,84989,"[MFT STD_INFO] Python26\Scripts\EASY_I~2.PY (Offset: 0x1042f400)"
Tue Oct 20 2009 12:08:06,0,ma.b,---a-----------,0,0,84990,"[MFT STD_INFO] Python26\Scripts\EASY_I~2.EXE (Offset: 0x1042f800)"
Tue Oct 20 2009 21:21:26,0,...b,---a-----------,0,0,66083,"[MFT STD_INFO] Documents and Settings\Administrator\Desktop\SysinternalsSuite\ZoomIt.exe (Offset: 0x1a8a5c00)"
Wed Oct 21 2009 00:02:28,76800,m...,---a-----------,0,0,65342,"[MFT FILE_NAME] Program Files\NTCore\Explorer Suite\Tools\DRIVER~1.EXE (Offset: 0x14b9c800)"
Wed Oct 21 2009 00:02:28,76800,m...,---a-----------,0,0,65342,"[MFT FILE_NAME] Program Files\NTCore\Explorer Suite\Tools\DriverList.exe (Offset: 0x14b9c800)"
Wed Oct 21 2009 00:02:28,76800,m...,---a-----------,0,0,65342,"[MFT STD_INFO] Program Files\NTCore\Explorer Suite\Tools\DRIVER~1.EXE (Offset: 0x14b9c800)"
Wed Oct 21 2009 18:25:52,780800,m...,---a-----------,0,0,65338,"[MFT FILE_NAME] Program Files\NTCore\Explorer Suite\TASKEX~1.EXE (Offset: 0x14b1b800)"
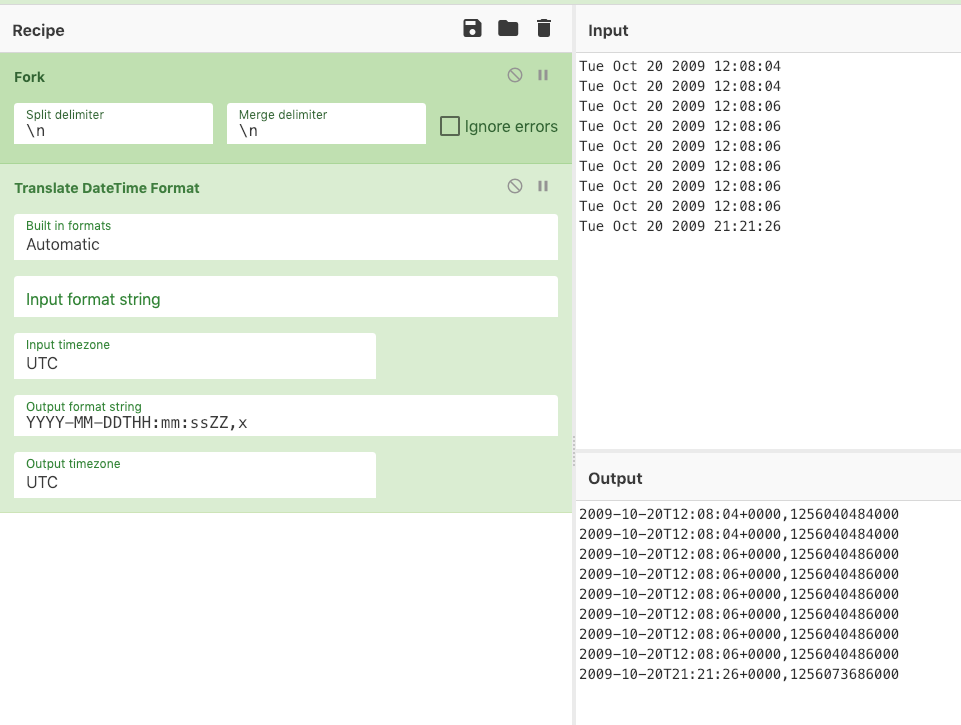
so we need to adjust that. In the past, I used an own developed python script https://github.com/deralexxx/timesketch-tools/tree/master/date_converter for that, but that does not really scale, so I considered another option.
Cyberchef
An open source tool by GCHQ: https://gchq.github.io/CyberChef/
A simple, intuitive web app for analysing and decoding data without having to deal with complex tools or programming languages. CyberChef encourages both technical and non-technical people to explore data formats, encryption and compression.
https://gchq.github.io/CyberChef/#about
Installation
git clone https://github.com/gchq/CyberChefhttps://github.com/gchq/CyberChef/wiki/Getting-started
Now open it
From the CSV that was generated, use your favourite tool to extract the first column of the csv which should look like that:
Date
Tue Oct 20 2009 12:08:04
Tue Oct 20 2009 12:08:04
Tue Oct 20 2009 12:08:06
Tue Oct 20 2009 12:08:06
Tue Oct 20 2009 12:08:06
Tue Oct 20 2009 12:08:06
Tue Oct 20 2009 12:08:06
Tue Oct 20 2009 12:08:06
Tue Oct 20 2009 21:21:26
Wed Oct 21 2009 00:02:28Now use the following CyberChef Recipe
Fork('\\n','\\n',false)
Translate_DateTime_Format('Automatic','','UTC','YYYY-MM-DDTHH:mm:ssZZ,x','UTC')And paste them all into input. It will result in a file you can download with the output.
Now the output txt has two CSV columns, you need to combine them with your autotimeliner csv to have the following headers:
datetime timestamp timestamp_desc
2009-10-20T12:08:04+0000 1256040484000 stuxnet.vmem_Mem_Dump_Timeline
2009-10-20T12:08:04+0000 1256040484000 stuxnet.vmem_Mem_Dump_Timeline
2009-10-20T12:08:06+0000 1256040486000 stuxnet.vmem_Mem_Dump_Timeline
2009-10-20T12:08:06+0000 1256040486000 stuxnet.vmem_Mem_Dump_Timeline
2009-10-20T12:08:06+0000 1256040486000 stuxnet.vmem_Mem_Dump_Timeline
2009-10-20T12:08:06+0000 1256040486000 stuxnet.vmem_Mem_Dump_TimelineNow the csv should like like:
more stuxnet.vmem.zip/stuxnet.vmem-timeline_timesketch.csv
datetime,timestamp,timestamp_desc,Date,Size,Type,Mode,UID,GID,Meta,message
2009-10-20T12:08:04+0000,1256040484000,stuxnet.vmem_Mem_Dump_Timeline,Tue Oct 20 2009 12:08:04,0,ma.b,---a-----------,0,0,84995,[MFT STD_INFO] Python26\Lib\SITE-P~1\setuptools-0.6c11-py2.6.egg-info\TOP_LE~1.TXT (Offset: 0x8a28c00)
2009-10-20T12:08:04+0000,1256040484000,stuxnet.vmem_Mem_Dump_Timeline,Tue Oct 20 2009 12:08:04,0,ma.b,---a-----------,0,0,85000,[MFT STD_INFO] Python26\Lib\SITE-P~1\SETUPT~1.EGG\DEPEND~1.TXT (Offset: 0x75e4000)
2009-10-20T12:08:06+0000,1256040486000,stuxnet.vmem_Mem_Dump_Timeline,Tue Oct 20 2009 12:08:06,0,m..b,---a-----------,0,0,84985,[MFT STD_INFO] Python26\Scripts\EASY_I~1.PY (Offset: 0x91b9400)
There is one little caveat, you need to add „“ around the message, because some values might break the Import process.
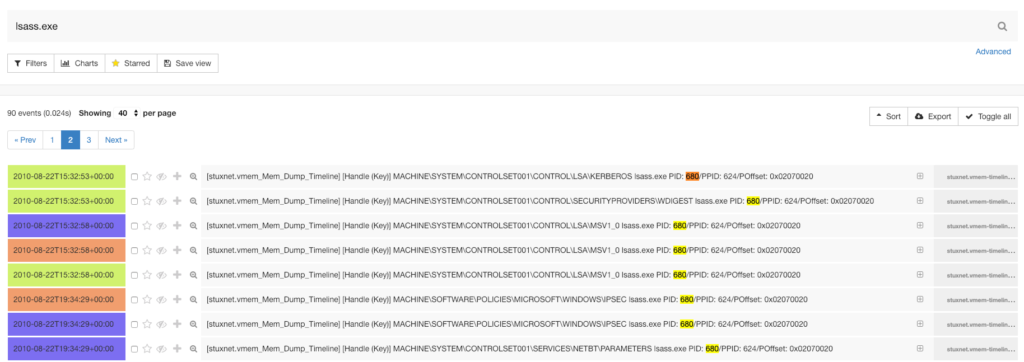
That can now be imported into Timesketch

Et voila, a timesketched Memory Dump